Account & Network Integrity Inspection for mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, and Njgcrby emphasizes disciplined governance of identities and network boundaries. The discussion centers on detecting endpoint and network anomalies, validating risks, and enforcing segmentation with auditable trails. The approach is meticulous and scalable, outlining practical controls and rapid-response actions. It leaves unresolved questions about prioritization and automation strategies, inviting focused consideration on where to begin and how to measure progress.
What Is Account & Network Integrity Inspection and Why It Matters
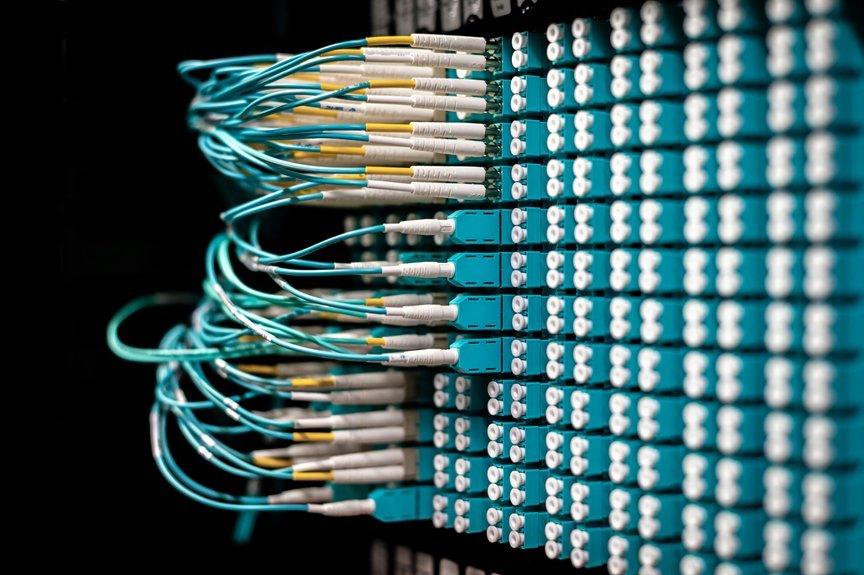
Account and Network Integrity Inspection involves systematically evaluating an organization’s digital environments to verify that user accounts and network infrastructure are secure, functional, and compliant with established policies.
It emphasizes rigorous governance of Account integrity and Network integrity, identifies Endpoints anomalies, enforces Network segmentation, and strengthens Identity controls.
Auditable trails enable Rapid response and guide Compliance actions with disciplined, transparent procedures.
Detecting Anomalies Across Endpoints and Networks
Analysts map risks to network segmentation boundaries, isolating suspicious activity, validating alerts, and ensuring auditable trails while maintaining operational freedom and minimal disruption to legitimate workflows.
Implementing Identity Controls, Segmentation, and Auditable Trails
The approach infers privacy-aware policies, mitigates risk, and supports auditable trails.
It highlights detect anomalies, enforce least privilege, and ensure compliance, while remaining transparent to stakeholders who value operational freedom and disciplined governance.
Practical, Scalable Actions for Rapid Response and Compliance
Detect rogue devices, revoke access promptly, document actions, and audit outcomes.
Continuous refinement, automation, and cross-functional coordination sustain resilience and freedom within disciplined rigor.
Conclusion
Meticulous, methodical measures maximize management of mumflexsai4, nbllas95233wm, nhbgvfqlhbv, nishidhasagamam, and njgcrby. Vigilant vision validators verify volatile vaults, vendors, and vectors, safeguarding segmentation and system boundaries. Deliberate detection drives disciplined decisions, documenting deviations, delineating duties, and delivering dependable dashboards. Prudent protocols prioritize prompt pinpointing, precise provisioning, and persistent pruning of pernicious paths. Continuous calibration cultivates compliance, coordination, and cross-functional clarity, culminating in a resilient, repeatable, and reliable account-and-network integrity framework.