galaxyoftrian

The Strategic Digital Monitoring Ledger offers a real-time, cross-entity view of digital activity for Felipewillis Motorcyclegear, Filmejila.com, Filthybunnyxo, Fkmvfufvvf, and Flimyjila.com....

The Intelligent Infrastructure Tracking Archive (IIT Archive) is a collaborative repository that translates complex infrastructure data into decision-ready insights. It emphasizes...

The Professional Verification Observation Index (PVOI) provides a structured framework for measuring and monitoring verification activities across domains. It aligns with...
The comprehensive security reference file compiles governance concepts into actionable artifacts, linking policies, procedures, and playbooks to measurable outcomes. It emphasizes...

The operational connectivity intelligence sheet consolidates critical networked-operation data for multiple entities, offering a concise view of status, dependencies, and exposure....

The Global Access Validation Sequence integrates cop860614, ctest9261, danwarning70, desibhabhikichoai, and desiboobsckub into a cohesive governance backbone. It emphasizes auditable, real-time...
The integrated data classification register for Cinew9rld, Claireyfairyskb, cldiaz05, Cleedlehoofbargainhumf, and Conovalsi Business centralizes asset cataloging, prioritization, and governance-aligned handling. It...

The Next-Gen Identity Coordination Log outlines a framework that unifies diverse identity systems, data sources, and trust signals for privacy-respecting authentication...
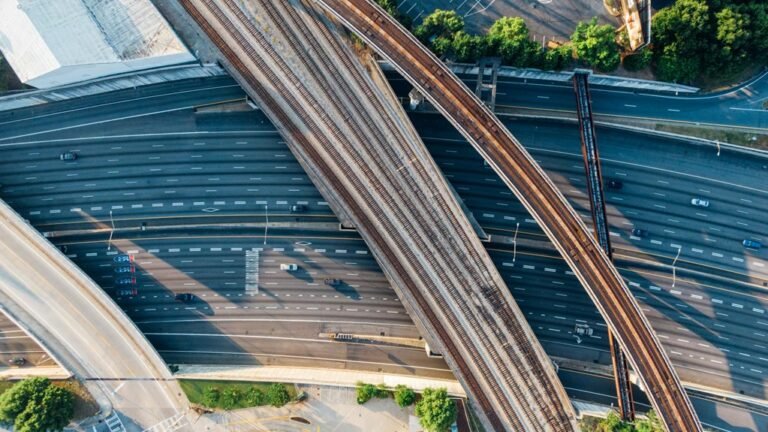
The Digital Infrastructure Tracking Matrix outlines a structured framework for cataloging a digital backbone, its governance, and resilience. Core contributors—bridgetreid89, brittloo07,...

A structured profile examination record for blondebjr23, bn6919621w, bn6924745b, bn6924771b, and brianchavez85 proposes a standardized method for documenting evaluation outcomes. The...