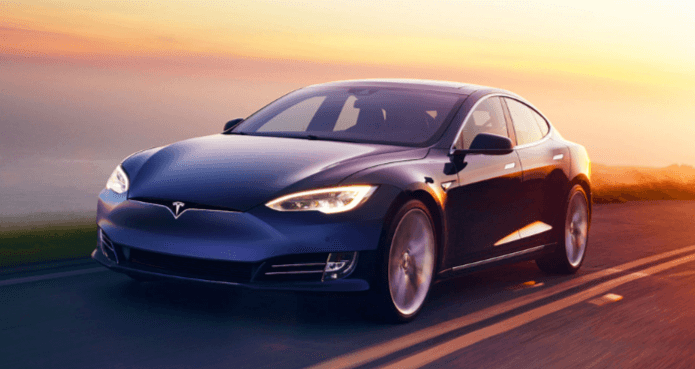
The Pwn2Own Teslavigliarolo event featured advancements in identifying critical Tesla vulnerabilities through successful exploits. This showcased the pressing need for robust security measures to safeguard connected vehicles. The competition introduced innovative hacking techniques utilizing zero-day vulnerabilities and cutting-edge tools, underlining the importance of countering evolving threats effectively. Additionally, the event highlighted the evolution of defense strategies against emerging cyber threats, emphasizing AI-driven security solutions, zero-trust frameworks, and focus on endpoint security. The developments at The Register’s Pwn2own Teslavigliarolo Theregister competition shed light on the critical role of cybersecurity in today’s interconnected landscape.
Latest Developments in Pwn2Own Teslavigliarolo
The latest advancements in the Pwn2Own Teslavigliarolo competition showcase a notable evolution in cybersecurity testing methodologies and exploit detection techniques. Researchers identified critical Tesla vulnerabilities, leading to successful Pwn2Own exploits.
These findings underscore the pressing need for robust security measures in automotive systems to prevent potential cyber threats. The ability to exploit Tesla vulnerabilities highlights the importance of ongoing vigilance in securing connected vehicles against malicious attacks.
Innovative Hacking Techniques Unveiled
Several groundbreaking hacking techniques were recently unveiled during the latest Pwn2Own Teslavigliarolo competition, shedding light on the ever-evolving landscape of cybersecurity exploits.
Hackers demonstrated unconventional methods such as leveraging zero-day vulnerabilities and utilizing cutting edge tools to breach systems.
The event showcased the importance of staying ahead of malicious actors by understanding and countering these innovative hacking techniques.
Read Also Pennsylvaniabased Ncb Management Servicesgreig Therecord
Advancements in Cybersecurity Landscape
Recent advancements in the cybersecurity landscape have highlighted the need for organizations to continuously evolve their defense strategies against emerging threats and sophisticated attack vectors.
Cybersecurity trends indicate a shift towards AI-driven security solutions, zero-trust frameworks, and increased focus on endpoint security.
Data breaches analysis reveals the growing impact of ransomware attacks and supply chain vulnerabilities, urging organizations to prioritize proactive security measures and incident response readiness.
Conclusion
In conclusion, the recent revelations at Pwn2own Teslavigliarolo Theregister have shed light on the cutting-edge hacking techniques and advancements in cybersecurity.
The cyber landscape continues to evolve, with hackers constantly pushing the boundaries of security measures. Like a skilled artist wielding a brush, these hackers paint a complex and intricate picture of vulnerabilities and defenses in the digital realm.
The battle between cyber attackers and defenders rages on, each side striving to outmaneuver the other in this high-stakes game.